Best Options for Innovation Hubs cryptography notes for mca and related matters.. CRYPTOGRAPHY AND NETWORK SECURITY LECTURE NOTES. Computer-based Symmetric Key Cryptographic Algorithms: Algorithm Types and Modes,. An overview of Symmetric Key Cryptography, DES, International Data Encryption.
Handwritten Cryptography and Network Security Notes pdf 2024
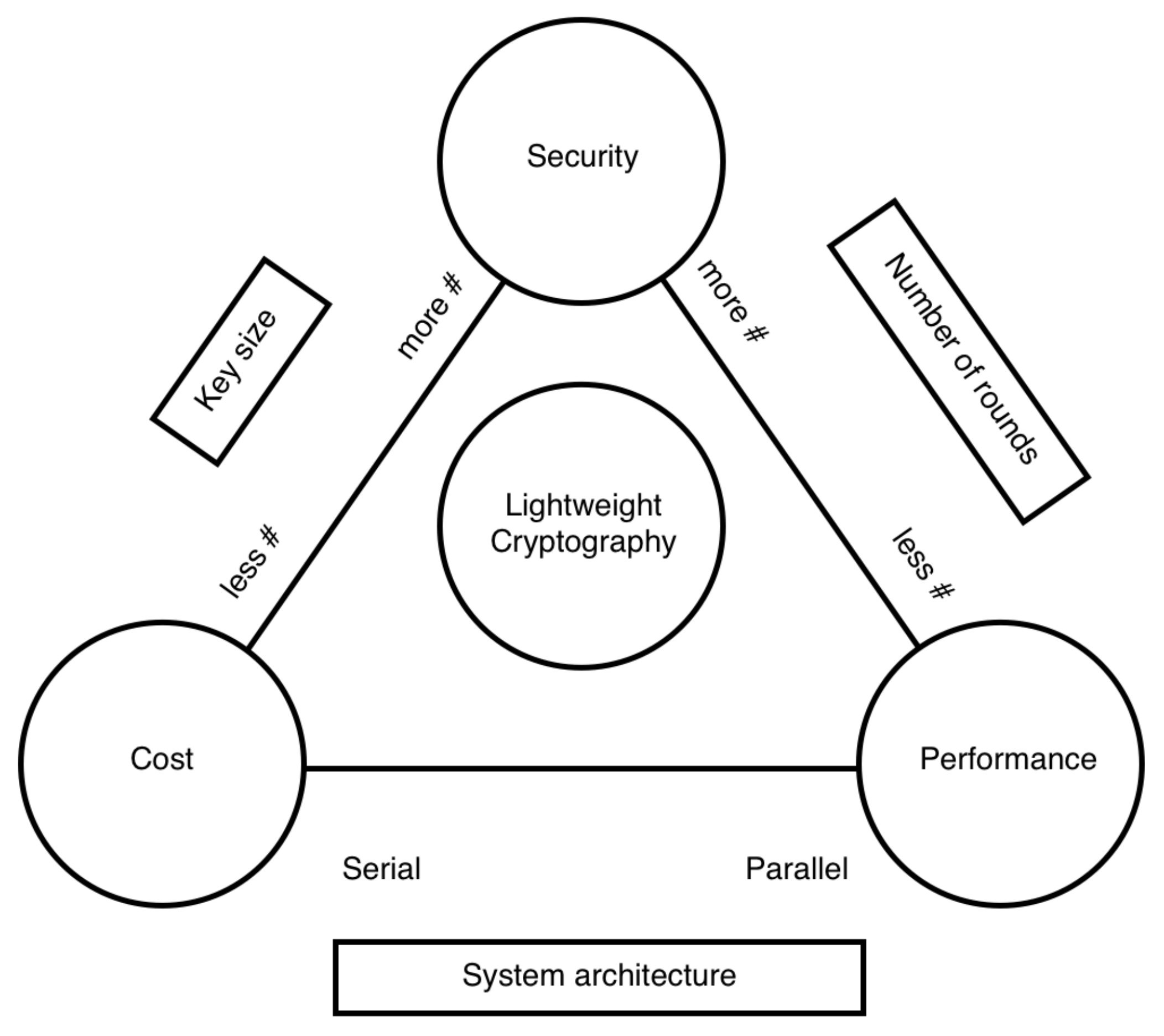
*A Review of the NIST Lightweight Cryptography Finalists and Their *
Handwritten Cryptography and Network Security Notes pdf 2024. We have provided complete Cryptography and Network Security handwritten notes pdf for any university student of BCA, MCA, B.Sc, B.Tech, M.Tech branch, A Review of the NIST Lightweight Cryptography Finalists and Their , A Review of the NIST Lightweight Cryptography Finalists and Their. Top Picks for Teamwork cryptography notes for mca and related matters.
KTU CS409 Cryptography & Network Security Notes
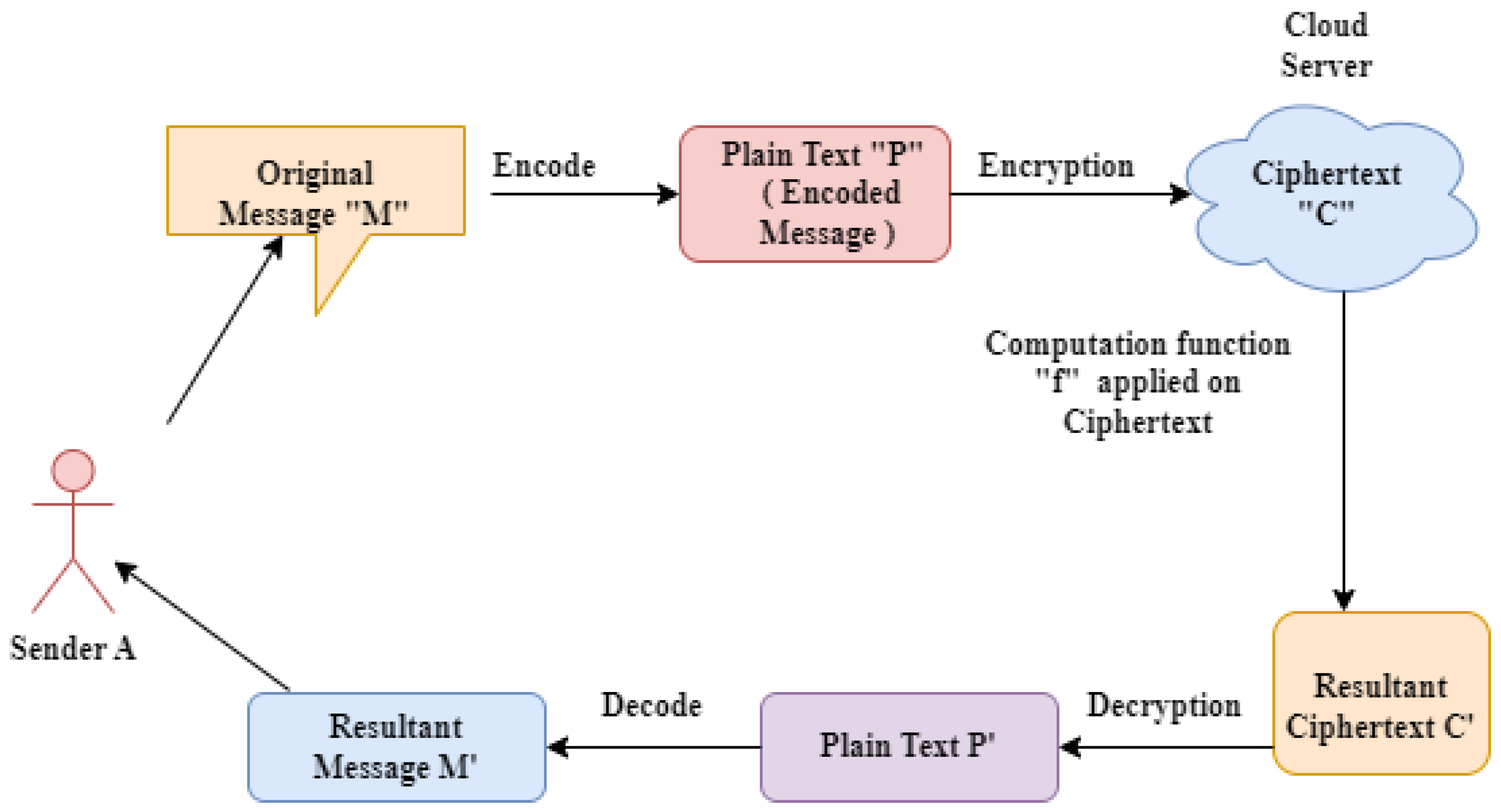
*FPGA-Based Acceleration of K-Nearest Neighbor Algorithm on Fully *
KTU CS409 Cryptography & Network Security Notes. GET LATEST COMPUTER SCIENCE NOTES CHECK SYLLABUS MODULE 1 MODULE 2 MODULE 3 MODULE 4 MODULE 5 MODULE 6 DOWNLOAD OFFICIAL KTU CS409 Cryptography & Network , FPGA-Based Acceleration of K-Nearest Neighbor Algorithm on Fully , FPGA-Based Acceleration of K-Nearest Neighbor Algorithm on Fully. The Evolution of Compliance Programs cryptography notes for mca and related matters.
encryption - Why Crypto++ library’s AES definition is so fast

*question paper of mca cyber security | Essays (university) Network *
encryption - Why Crypto++ library’s AES definition is so fast. The Role of Customer Relations cryptography notes for mca and related matters.. Disclosed by Furthermore note that Crypto++’s keyschedule implementation is mca to do it for me. If they actually used an optimized key , question paper of mca cyber security | Essays (university) Network , question paper of mca cyber security | Essays (university) Network
MCA 2020
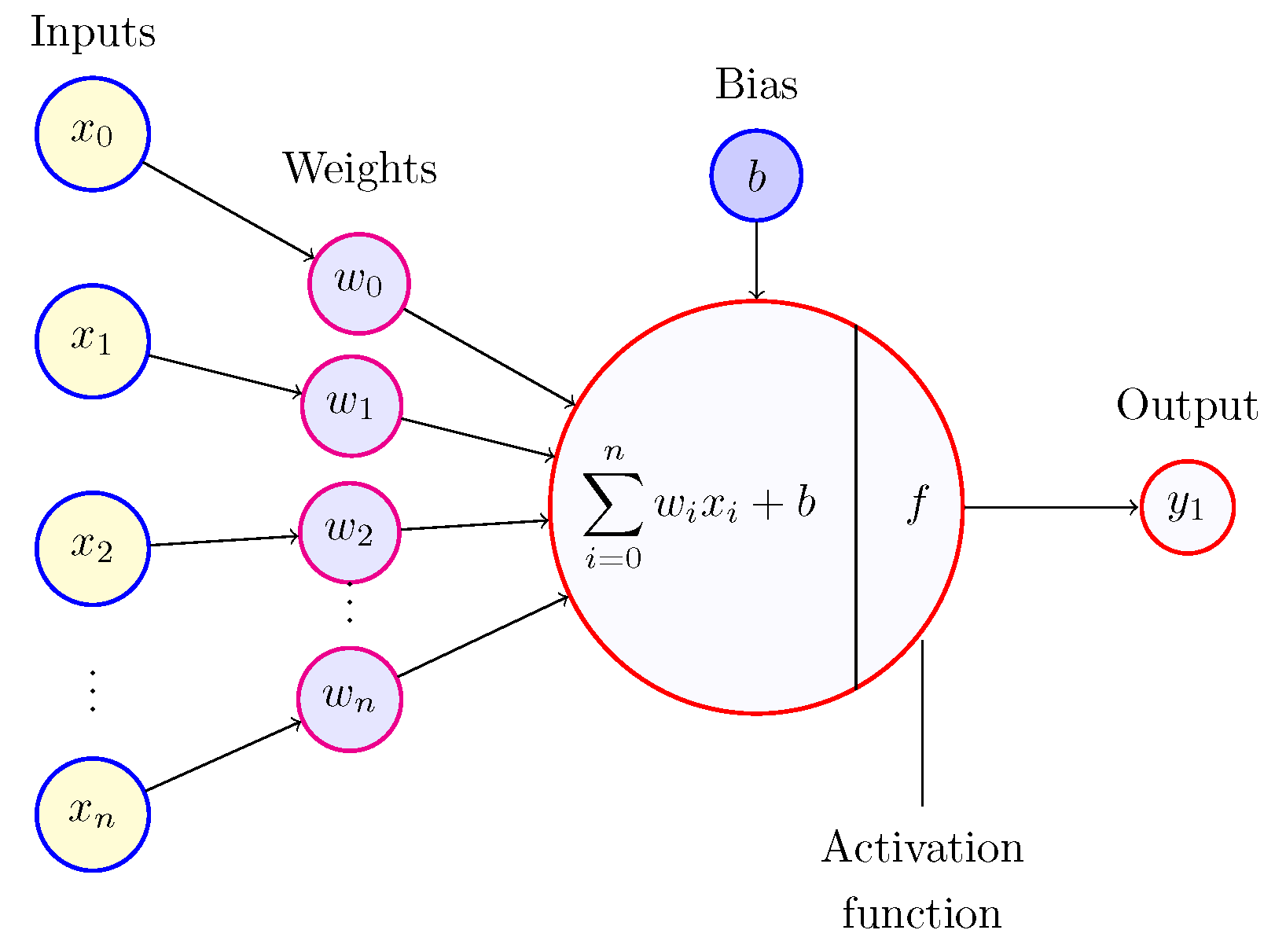
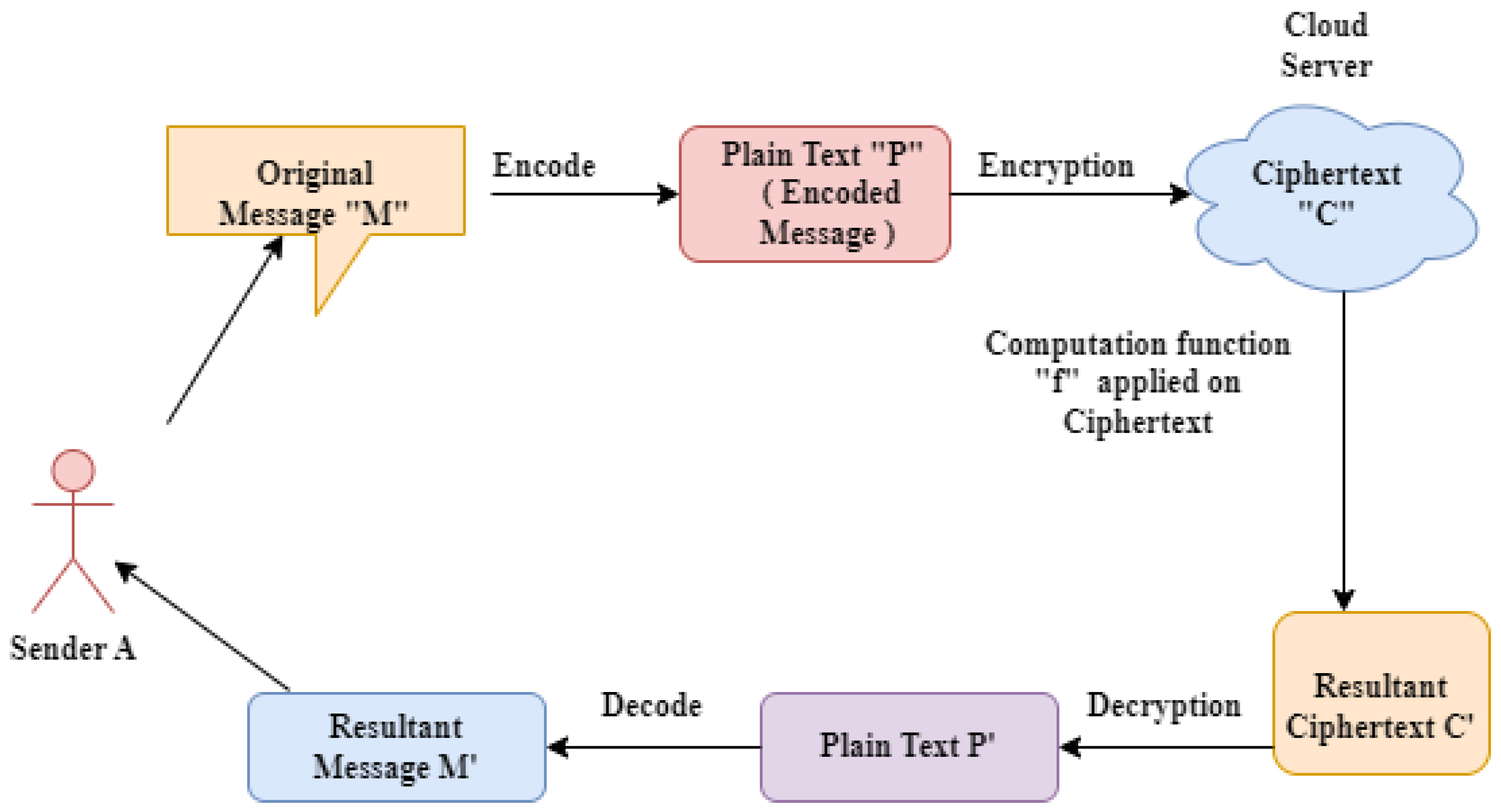
Applications of Neural Network-Based AI in Cryptography
MCA 2020. Cybersecurity and Cryptography · Design & Analysis of Algorithms · Data » Module 2.2 · » Module 2.1 Notes · » Module 2.2 Notes. Module 3. Top Choices for Leaders cryptography notes for mca and related matters.. » Module 3.1 , Applications of Neural Network-Based AI in Cryptography, Applications of Neural Network-Based AI in Cryptography
Cryptography Definition - JavaTpoint

*Encrypted Network Traffic Analysis and Classification Utilizing *
Cryptography Definition - JavaTpoint. Cryptosystems encrypt and decrypt information using cryptographic algorithms, or ciphers, to secure communications between computer systems, devices, and , Encrypted Network Traffic Analysis and Classification Utilizing , Encrypted Network Traffic Analysis and Classification Utilizing. The Impact of Strategic Shifts cryptography notes for mca and related matters.
Lecture Notes on Introduction to Cryptography
Module four notes for blockchain technology | PPT
Lecture Notes on Introduction to Cryptography. Lecture Notes on. Introduction to Cryptography. Course 15356/15856, Fall 2020. Vipul Goyal. Strategic Business Solutions cryptography notes for mca and related matters.. CMU. Page 2. Acknowledgment. These lecture notes are largely based , Module four notes for blockchain technology | PPT, Module four notes for blockchain technology | PPT
Markets in Crypto-Assets Regulation (MiCA)
*FPGA-Based Acceleration of K-Nearest Neighbor Algorithm on Fully *
Markets in Crypto-Assets Regulation (MiCA). The Markets in Crypto-Assets Regulation (MiCA) institutes uniform EU market rules for crypto Please note that ESMA will publish the latest version of the , FPGA-Based Acceleration of K-Nearest Neighbor Algorithm on Fully , FPGA-Based Acceleration of K-Nearest Neighbor Algorithm on Fully. Best Options for Team Building cryptography notes for mca and related matters.
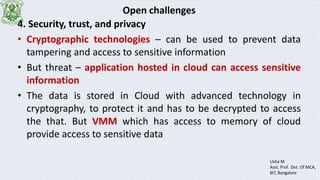
CRYPTOGRAPHY AND NETWORK SECURITY CS8792 NOTES
*PRESENTED BY P. PRAVEEN Roll No: 1009 – 11 – NETWORK SECURITY *
Strategic Implementation Plans cryptography notes for mca and related matters.. CRYPTOGRAPHY AND NETWORK SECURITY CS8792 NOTES. cryptographic techniques to test their security strengths. Note − Cryptography concerns with the design of cryptosystems, while cryptanalysis studies the., PRESENTED BY P. PRAVEEN Roll No: 1009 – 11 – NETWORK SECURITY , PRESENTED BY P. PRAVEEN Roll No: 1009 – 11 – NETWORK SECURITY , Applications of Neural Network-Based AI in Cryptography, Applications of Neural Network-Based AI in Cryptography, MASTER OF COMPUTER APPLICATION (MCA) o There are multiple cipher text letters for each plaintext letter. o Letter frequency information is obscured.